Want to see your organization in DevOps’ish? Review the newsletter sponsor page for all the details. Give the DevOps’ish Sponsorship Prospectus a gander if you need help convincing your marketing team they should spend. SPONSORED
DevOps’ish is brought to you by Accurics. They’re cool people doing cool things with cloud native security. Check them out! Scanning Kubernetes IaC configurations with Terrascan
People
The 2020 Last Week in AWS Charity T-Shirt: Route53
I always love it when people ask if I know Corey Quinn. Yes, we’re friends on two different sides of the country (we have the technology, it is possible). Our kids played piano together last year on our family trip to San Francisco and Yosemite. I bought Max the San Francisco LEGO set for his birthday this week because that trip made such an impact on him as a person. The Quinn Family played a huge part of that. Corey is on my incredibly short Christmas card list. When my friends are trying to do good in the world I like to highlight that. Please, buy a t-shirt, tack on an extra $10 if you can, and support an amazing cause in 826 National.
fluxcd/community
“The Flux project aspires to be a vendor-neutral home for GitOps in a Cloud Native world.”
Write Down Your Team’s Unwritten Rules
“During stressful times (i.e. right now), it’s good practice to write down the unstated cultural and emotional norms that exist within your team or company. They might have changed since you all started working from home, or perhaps they’ve never been explicit to everyone.”
Lesley Carhart: if the shirt fits, or even if it doesn’t, wear it
“When Lesley Carhart joined a start-up in the early 2000s, she was the first woman there to work in a technical role. That became obvious when she went to the marketing office to pick up her company shirts, required for anyone interacting with clients. The company didn’t have shirts for women. Instead, there were men’s shirts sizes large through extra, extra-large.”
The Unsinkable Maddie Stone, Google’s Bug-Hunting Badass
“The Project Zero reverse engineer shuts down some of the world’s most dangerous exploits—along with antiquated hacker stereotypes.”
How Google Cloud’s Kelsey Hightower became one of the most respected people in cloud computing
“A self-taught technologist with a storyteller’s voice, Kelsey Hightower defied the enterprise tech sector’s notorious diversity problems to become one of the industry’s leading figures. Now he wants everyone’s voice to be heard.”
Process
People might say traces can be used anywhere, but let’s face it: you absolutely need them when you’re dealing with distributed systems and microservices. You probably don’t have them yet because instrumenting your apps to collect them will get you super table-flippy. (╯°□°)╯︵ ┻━┻
Until now.
Download Distributed Tracing: A Guide to Microservices & More and get the tracing you deserve the easy peasy way. Guess less & know more with Honeycomb. SPONSORED
In a first, researchers extract secret key used to encrypt Intel CPU code
“For now, there’s only one but very important consequence: independent analysis of a microcode patch that was impossible until now,” Positive Technologies researcher Mark Ermolov said. “Now, researchers can see how Intel fixes one or another bug/vulnerability. And this is great. The encryption of microcode patches is a kind of security through obscurity.”
Pulumi raises Series B to build the future of Cloud Engineering
Popular IaC tool company gets funding round.
AMD Acquiring Xilinx In Bold, $35B Semiconductor Mega-Deal
“AMD and Xilinx have hugely different product portfolios and are focused on different markets with a few exceptions. That is a good thing when it comes to acquisitions and I believe the two companies are complementary.”
The Future of Cloud Native Security Is Self-Healing
“Whether you’re motivated by your obligation to users or your legal obligations, the goal is the same: to prevent breaches. More specifically, to reduce the opportunity for failure while delivering secure products more consistently.”
How to waste half a day by not reading RFC 1034
“Plenty of other companies have implemented their own version of branch deploys (typically under a different name), but this was my own implementation, so I’m proud of it.”
Tools
Oh Dear, uptime monitoring like no other
With Oh Dear, you get uptime monitoring, SSL certificate alerts, performance monitoring and we’ll crawl your entire site, reporting 404’s, server errors and more. With our unlimited status pages and cron job monitoring, Oh Dear is all the monitoring you’ll ever need. Sign up with code DEVOPSISH and get a 30% discount on your first 3 months. SPONSORED
Phantom Analyzer
A simple, real-time website scanner to see what invisible creepers are lurking in the shadows and collecting information about you.
Link Previews: How a Simple Feature Can Have Privacy and Security Risks
So much wasted bandwidth and CPU not to mention lack of privacy in a lot of cases.
RIAA’s YouTube-DL Takedown Ticks Off Developers and GitHub’s CEO
“An RIAA takedown request, which removed the YouTube-DL repository from GitHub, has ticked off developers and GitHub’s CEO. Numerous people responded by copying and republishing the contested code, including in some quite clever ways. Meanwhile, GitHub’s CEO is “annoyed” as well, offering help to get the repo reinstated.”
Music industry forces widely used journalist tool offline
“In fact, youtube-dl is a powerful general purpose media tool that allows users to make local copies of media from a very broad range of sites. That versatility has secured it a place in the toolkits of many reporters, newsroom developers, and archivists.”
‘Deciphering’ YouTube’s Rolling Cypher in Your Browser is a Piece of Cake
“The RIAA and other music groups recently accused youtube-dl and related stream-ripping tools of circumventing YouTube’s ‘rolling cipher’ protection. While that may sound complex, anyone can download full audio and video files from YouTube, using nothing more than a web browser. It’s surprisingly easy and we failed to spot any ciphers.”
Systemd 247-RC1 Released With Systemd-OOMD, Systemd-Homed Now Defaults To Btrfs
“This big systemd 247 release is introducing systemd-oomd for out-of-memory daemon handling, systemd-homed now defaults to using Btrfs, there is a new capability with systemd of secure credentials handling, and much more.”
PromQL for Humans
“PromQL is a built in query-language made for Prometheus. Here at Timber we’ve found Prometheus to be awesome, but PromQL difficult to wrap our heads around. This is our attempt to change that.”
Apache Kafka on Kubernetes with Strimzi - Part 3: Monitoring our Strimzi Kafka Cluster with Prometheus and Grafana
This three part series is a wonderful one. I highly recommend giving it a once over.
Goodbye IFTTT
Yup, with recent changes and new advances, IFTTT is falling out of favor with a lot of folks.
stackrox/kube-linter
“KubeLinter is a static analysis tool that checks Kubernetes YAML files and Helm charts to ensure the applications represented in them adhere to best practices.” StackRox also wrote a blog post about kube-linter. My take, this is a pretty big step forward for an organization that a year ago did not have an open source offering at all. I hope to see more companies releasing tools that make their engineers more productive in the cloud native security landscape. I’ll be continuing to kick the tires on this as the week progresses.
lirantal/awesome-nodejs-security
Awesome Node.js Security resources
rebuy-de/aws-nuke
Nuke a whole AWS account and delete all its resources.
cloud-custodian/cloud-custodian
Rules engine for cloud security, cost optimization, and governance, DSL in yaml for policies to query, filter, and take actions on resources
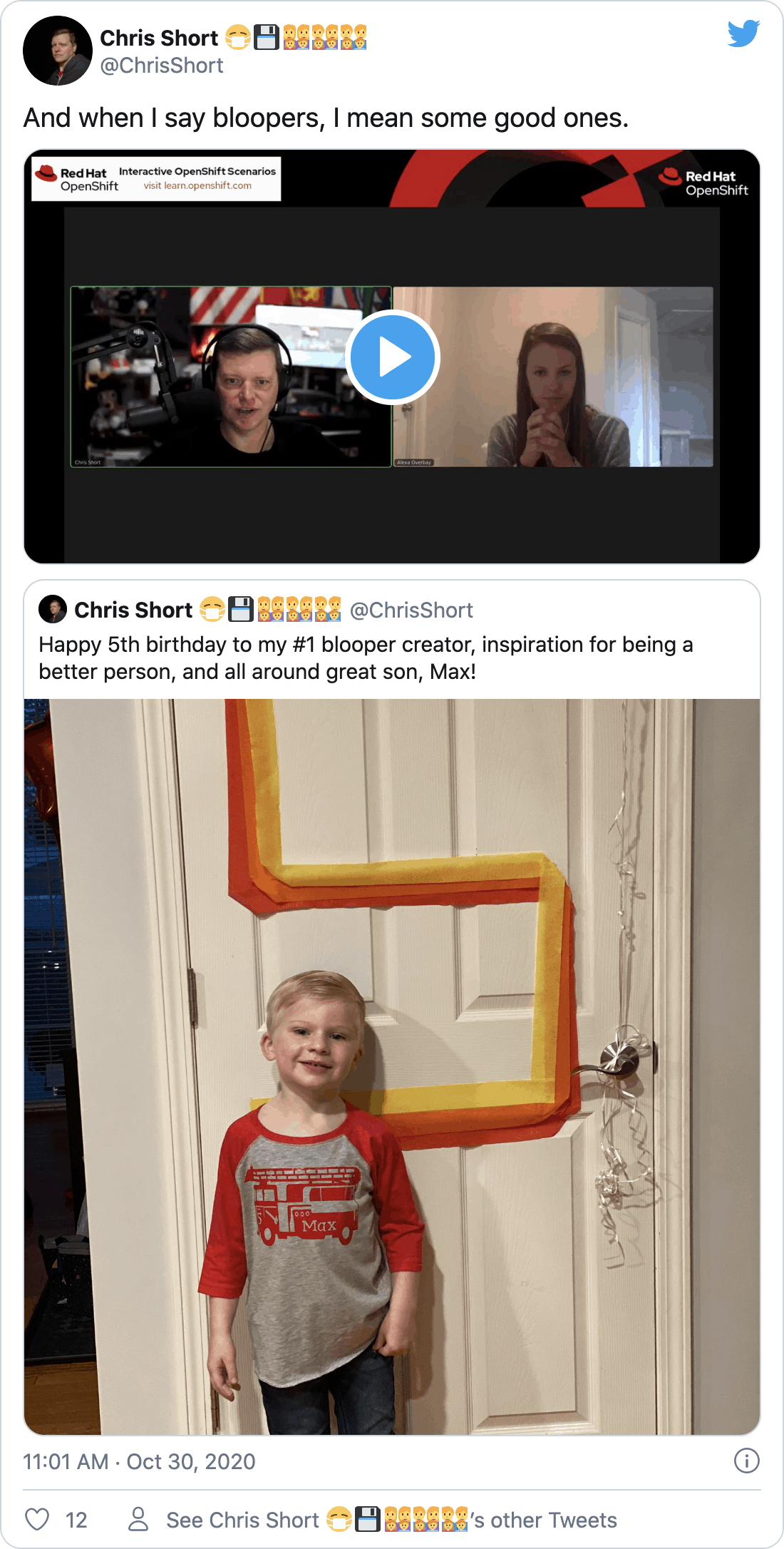
DevOps’ish Tweet of the Week
Want more? Be sure to check out the notes from this week’s issue to see what didn’t make it to the newsletter.