Remember last week how I said things would be punchier? Well, I updated the DevOps’ish Solarwinds supply chain compromise Index. By the way, Microsoft says it was, “used by a different threat actor.”
I wrote the parts of the newsletter below, which are probably helpful. ¯\_(ツ)_/¯
The past few days have been incredibly challenging mentally and physically. I’m not sure if I would do it all the same way again. Sadly, I think I’m going to have to sideline myself a little more next year. The good news is, I get to try again next year. For that, I am truly thankful. The holidays, especially religious-based ones, are challenging for me. I have a challenging relationship with religion in general. That’s for a different blog though. For those celebrating holidays the past few weeks and the weeks ahead, I wish you all the best.
DevOps’ish is brought to you by Accurics
People
Reverse Engineering the source code of the BioNTech/Pfizer SARS-CoV-2 Vaccine
“In this post, we’ll be taking a character-by-character look at the source code of the BioNTech/Pfizer SARS-CoV-2 mRNA vaccine.” Damn. That’s awesome.
Our Digital Lives Drive a Brick-and-Mortar Boom in Data Centers
“Developers and investors see more opportunities in commercial real estate as businesses and consumers gobble up more data.”
The Secret History of the First Microprocessor, the F-14, and Me
There was the Intel 4004, then there was this monster. This is a great story that I’m glad has come to light.
GoDaddy Employees Were Told They Were Getting a Holiday Bonus. It Was Actually a Phishing Test.
I haven’t used GoDaddy in a LONG time. You shouldn’t either.
How Claude Shannon’s Information Theory Invented the Future
“The heart of his theory is a simple but very general model of communication: A transmitter encodes information into a signal, which is corrupted by noise and then decoded by the receiver. Despite its simplicity, Shannon’s model incorporates two key insights: isolating the information and noise sources from the communication system to be designed, and modeling both of these sources probabilistically.” I’ve touched this work with my own hands. Pushing signals to and fro, multiplexing them, sending them over the air only to be disassembled on the other side.
Process
Analyzing Solorigate, the compromised DLL file that started a sophisticated cyberattack, and how Microsoft Defender helps protect customers
Take a deep dive into the DLL toppling security apparatus across the globe. Also, it was “used by a different threat actor.” Oh good… Multiple agencies knew about it and exploited it. Sit back and grab your popcorn and keep an eye on the index.
How GitOps Improves the Security of Your Development Pipelines
“GitOps is usually discussed in terms of boosting developer velocity. But another benefit – one that doesn’t always get as much attention – concerns its potential to improve security.” To go fast, you have to go safely and securely. Otherwise, you’re introducing risk. You’re human. Let a computer and the knowledge of as many viable sources as possible do the safety and security for you. But that in the GitOps toolchain and maybe, you won’t end up like Solarwinds (aka on the front page of news sources the world over).
Apple Setup Issues: Apple Watch Verification Failed, HomePod Stuck on Configuring
How’s that switch from Mesos to Kubernetes coming? Oh… Distributed systems are hard.
Executable PNGs
Imagine this concept with a tight bit of Go or Rust logic. Large PNGs would be odd but not easily detected as suspicious without some actual compute looking into it.
Linux Hardening Guide
I would have killed for this web site in the early 2000s. Many arguments and old ways could’ve been avoided.
Tools
Active-Active PostgreSQL Federation on Kubernetes
This is kinda a dream come true if you build this right (the article doesn’t mention the physics involved: latency, for example). But, it does cover HA in all locations with a single operator so that’s dope.
We need your voice!
In partnership with the team at ClearPath Strategies, Honeycomb.io is collecting insights for changes in software development and operation practices across our industry. How do you see the world and what your team is doing?
Take the survey for a chance to win $500 from Apple, HelloFresh, or Fender. SPONSORED
How an obscure British PC maker invented ARM and changed the world
2021 is going to be an ARM filled year, to say the least.
How to Trace Linux System Calls in Production with Minimal Impact on Performance
“This blog post introduces perf and traceloop, two commonly used command-line tools, to help you trace system calls in a production environment.” Because running strace in prod is a last resort.
GopherCon 2020: Angelica Hill - Anyone Can Be A Gopher!
I’m not a coder by trade but I am a Gopher (language not protocol). It’s one of the most welcoming communities out there.
Evolving Container Security With Linux User Namespaces
In this post, we describe how Titus agents leverage user namespaces to improve the overall security of the Titus agent fleet.
2020 Time Zone Database (tzdata) changes
I’m fascinated by the concept of time. How it is truly a mangled thing by humans to fit our will and wreak havoc in our systems.
CrowdStrike/CRT
“This tool queries the following configurations in the Azure AD/O365 tenant which can shed light on hard to find permissions and configuration settings in order to assist organizations in securing these environments.”
so-fancy/diff-so-fancy
Good-lookin’ diffs. Actually… nah… The best-lookin’ diffs.
owncast/owncast
“Take control over your live stream video by running it yourself. Streaming + chat out of the box.”
stolk/freqtop
Monitor for the CPU Frequency Scaling under Linux.
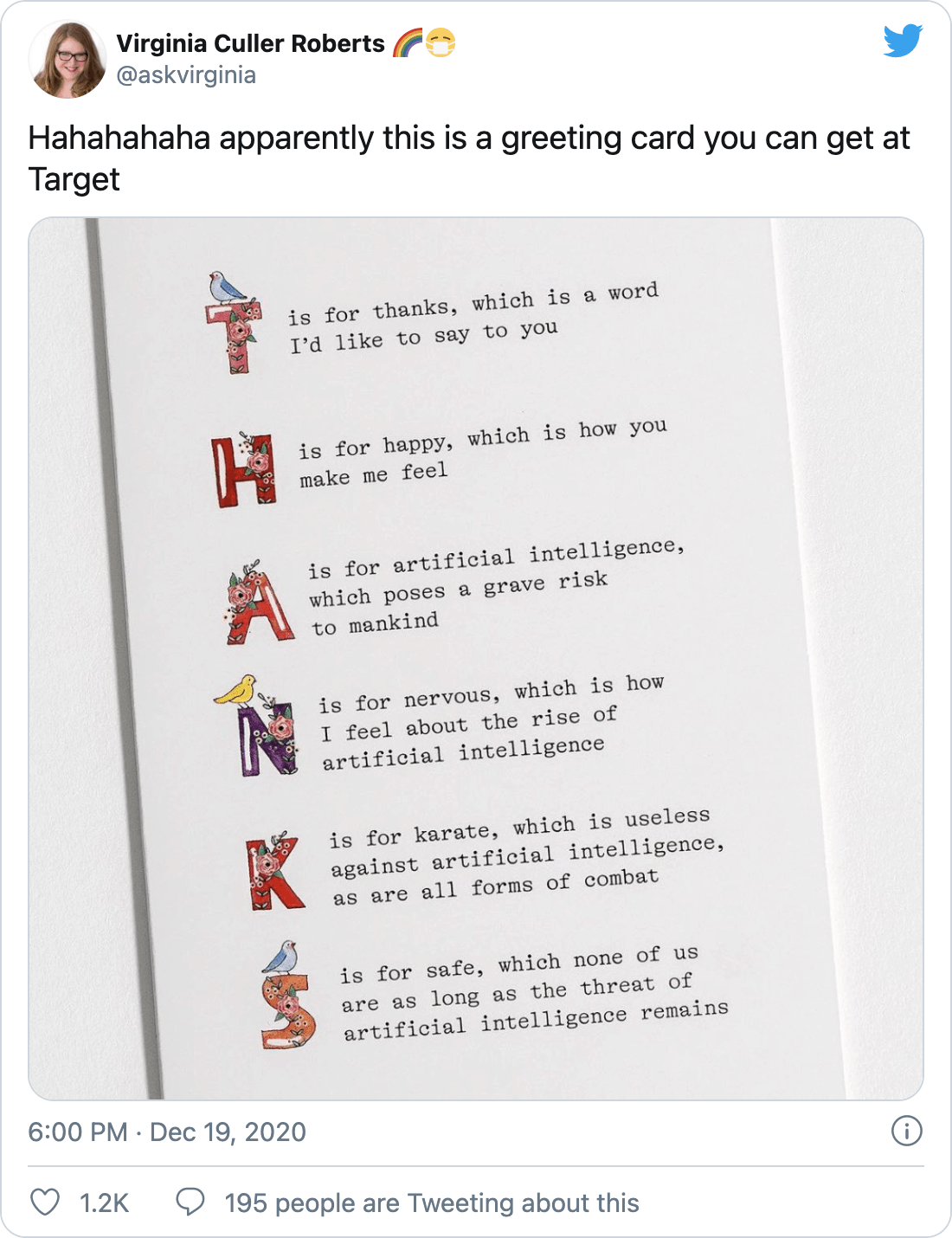
DevOps’ish Tweet of the Week
Want more? Be sure to check out the notes from this week’s issue to see what didn’t make it to the newsletter.