My military service and tech worlds collided this week. I can’t say much about it yet but, I’ve been insanely busy with an array of things I never thought I’d need to do. More to come later. Join the DevOps’ish subreddit and talk about how bad the intro was. Or how dope the notes page is for this issue.
People
Cloud Tech Tuesdays: Kubernetes 1.22
Josh Berkus, Amy Marrich, and I sat down for a livestream with Savitha Raghunathan, James Laverack, Jesse Butler, and Guinevere Saenger to discuss all things Kubernetes and the Kubernetes 1.22 release.
Free eBook: Docker Security Essentials by HackerSploit
Docker is a popular platform to quickly create, deploy and host web applications, databases and other business critical solutions. Learn how to audit and secure Docker in this comprehensive guide and 9-part video series. Download instantly – no registration required. SPONSORED
Samsung’s leader is out of jail, allowing US factory plans to move forward
“Samsung heir served 18 months in prison for capital flight and perjury.” Can someone that’s got a great understanding of Korean business and politics please reply to this email. I have no idea how this works and I want to understand it before I label it anything.
The Perl Foundation is fragmenting over Code of Conduct enforcement
It wasn’t that long ago that I learned there’s a lot more Perl out there than most folks realize. I wonder how sustainable that is NOW.
T-Mobile apparently lied to government to get Sprint merger approval, ruling says
This regulatory ruling stacked on top of multiple data breaches… T-Mobile needs a hard shaking it sounds like.
Sacklers say they won’t pay $4.5B settlement if judge rejects immunity deal
This is what happens to billionaires in the US. The Sacklers products reached so far and wide that the second-largest US administration regularly prescribed medications like morphine and fentanyl to its patients (leading to countless overdoses). It is utterly enraging for me. I’m a lucky survivor of the Sacklers’ opioid epidemic. Now I also deal with a rather undue process because I need an opioid to control pain from nerve damage. It’s a double slap in the face for those trying to live their lives with pain.
Process
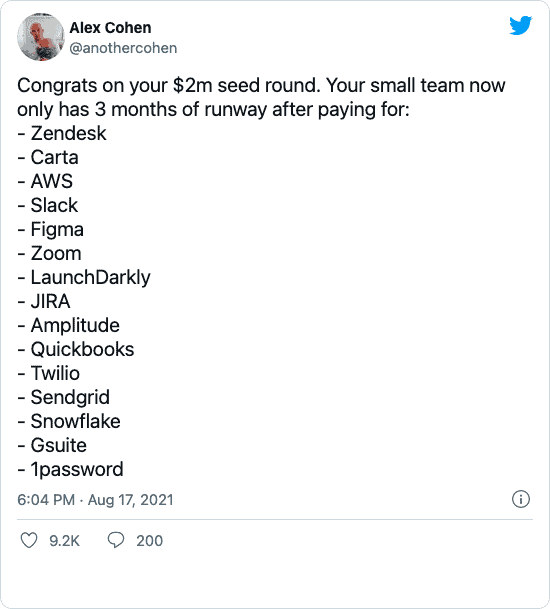
API platform Postman valued at $5.6 billion in $225 million fundraise
I like Postman. I occasionally use the tool for complex curl commands. But, I’ve got to say, I have no idea how Postman is valued at $5.6 billion. They’ve added a lot of integrations with common APIs. But, I am starting to think the bubble is real.
Infrastructure as Code Automation for Terrafrom and GitOps workflows
See how env0 automates and simplifies the provisioning of cloud deployments for Terraform. We offer Variables and Secrets granularity, Full CLI support, integration with OPA, Dynamic RBAC and SAML. Get Started for FREE! SPONSORED
Linux glibc security fix created a nastier Linux bug
“Sometimes a programming cure is worse than the disease. That’s the case with this Linux glibc security bug.” How one CVE’s fix lead to another CVE.
Patterns in confusing explanations
“So why do I find all these explanations so confusing? I decided to try and find out! I came up with a list of 12 patterns that make explanations hard for me to understand. For each pattern I’ll also explain what I like to do instead to avoid the issue.” This is GREAT reference material for when you’re writing docs, guides, READMEs, etc. My personal pet peeve is “no examples.”
The Absolute minimum every developer must know about AWS security!
Again, not all encompassing but, some decent recommendations and tooling are in this article. Remember, continuous security, always. You’re never done improving security just like you’re never done learning.
Email Authenticity 101: DKIM, DMARC, and SPF
Want to know why email is so hard these days? This article details why. If you don’t nail these three things, your email is bound for a spam folder.
Afghans are being evacuated via WhatsApp, Google Forms, or by any means possible
It’s complete chaos. There is a process. But, it’s burdensome and is likely limiting the number of people able to get out of the country.
Tools
StackRox Community Office Hours (E2): eBPF 101 — Implementing Security & Monitoring Kubernetes
Robby Cochran and I sat down for a livestream about eBPF. If you haven’t wrapped your head around eBPF yet, this is a great way to get started.
Making Your On-call and Incident Management Program Stick
Maintenance of your incident management practice is as important as creation - find out what you can do to keep your engineering organization strong and consistent year over year. SPONSORED
Hands on with Kubernetes Pod Security Admission
I’ll break my No Medium rule for Lachlan. “Kubernetes v1.22 provides an alpha release for the successor of Pod Security Policy (PSP) (which is scheduled for deprecation in v1.25). This new enhancement is called Pod Security Admission (PSA). I’ve taken an initial look at PSA and will cover what you need to know about how it works and how you can start playing with it. This will not be a deep dive into the architecture or reasoning behind the implementation. If you want to learn more about that you can find details in the Kubernetes Enhancement Proposal (KEP).”
Forthcoming OpenSSL release
“OpenSSL 1.1.1l is a security-fix release. The highest severity issue fixed in this release is HIGH.” Keep an eye on this one, folks.
Top 10 Kubernetes Application Security Hardening Techniques
A good overview of some of the security configurations available to you with Kubernetes. This should not be seen as an all encompassing hardening guide though. Use the CIS Benchmark, NSA Kubernetes Hardening Guide, or whatever framework your industry is required to use. If your industry isn’t regulated, I’d recommend implementing the CIS Benchmark if you haven’t yet (and if you haven’t hardened your clusters yet, I’ll probably see you in a headline in this newsletter soon).
Software Supply Chain Best Practices from CNCF TAG Security
Speaking of hardening, here are CNCF TAG Security’s supply chain recommendations. Build great pipelines, y’all.
Wildcard LetsEncrypt certificates with Traefik and Cloudflare
There’s some really great guides on using Let’s Encrypt with X and Z out there. Add this one to the list. Nice work, Major.
Pi calculated to ‘62.8 trillion digits’ with a pair of 32-core AMD Epyc chips, 1TB RAM, 510TB disk space
That’s A LOT of hardware and a lot of digits. The disk array was an interesting design too.
What domain name to use for your home network
This was a widely popular article this week. I’ve switched our home network over to home.arpa to see how this works. But, I have to say, I’ve not seen any significant problems. YMMV
How to automatically accept or disable browser cookies notice on any site
Cookie warnings have gotten completely out of control. This GDPR induced UX disaster has a solution or three though.
Add DC/OS End of Life message by jongiddy
Put a fork in DC/OS. It’s done.
kubealex/libvirt-ocp4-provisioner
“Automate your OCP4 installation” This could change the way I deploy my OpenShift clusters in the future. I wish I had more time to help refine projects like this.
dailymotion-oss/octopilot
“Automate your Gitops workflow, by automatically creating/merging GitHub Pull Requests”
iovisor/kubectl-trace
“Schedule bpftrace programs on your kubernetes cluster using the kubectl”
armosec/kubescape
“kubescape is the first tool for testing if Kubernetes is deployed securely as defined in Kubernetes Hardening Guidance by to NSA and CISA (https://www.nsa.gov/News-Features/Feature-Stories/Article-View/Article/2716980/nsa-cisa-release-kubernetes-hardening-guidance/)”
homeport/havener: /ˈheɪvənə/
“Think of it as a swiss army knife for Kubernetes tasks”
kubernetes-sigs/sig-windows-dev-tools
“This is a batteries included local development environment for Kubernetes on Windows.”
praetorian-inc/gokart
“A static analysis tool for securing Go code”
DevOps’ish Tweet of the Week
Want more? Be sure to check out the notes from this week’s issue to see what didn’t make it to the newsletter but are still worth your time.